Thank you for visiting my site!
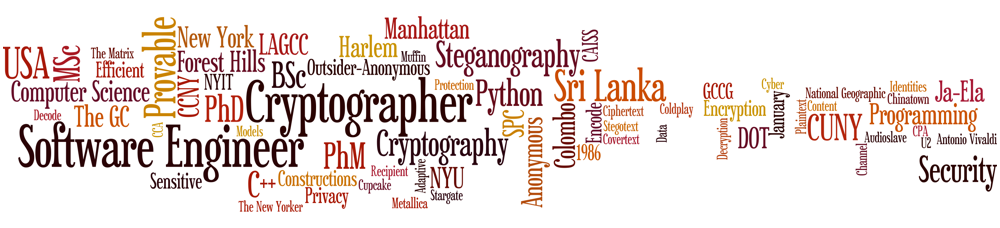
I earned my Ph.D. in Computer Science from the
Graduate Center of
CUNY in 2015,
where I had the privilege of working under the guidance of Professor
Nelly Fazio.
My research focused on the foundational theories, provable constructions, and practical applications of
Cryptography,
Steganography, and
Computer Security.
Since then, I've been at Google,
where I currently lead a team of software engineers in the User Protection organization.
We develop infrastructure that safeguards billions of Google users through advanced security
techniques like risk-based re-authentication and trust-based feature access. Our work protects
a wide range of users, including everyday consumers, content creators, journalists, political
figures, and business owners.
This site contains my published papers, talks, and other professional updates.
If you're interested in discussing cryptography, security, or any related topics,
I'm always open to connecting with like-minded professionals.
Feel free to reach out via email or connect with me on LinkedIn.
I welcome the opportunity to collaborate and share ideas in this exciting field. Looking forward to hearing from you!
Publications:
- KHyperLogLog: Estimating Reidentifiability and Joinability of Large Data at
Scale
Pern Hui Chia, Damien Desfontaines, Irippuge Milinda Perera, Daniel
Simmons-Marengo,
Chao Li, Wei-Yen Day, Qiushi Wang, and Miguel Guevara
IEEE Symposium on Security and Privacy – SP 2019, pp. 350-364, IEEE,
2019
[ paper | ieee ]
- Oblivious Group Storage
Nelly Fazio, Antonio R. Nicolosi, and Irippuge Milinda Perera
The Annual Conference of International Technology Alliance – ACITA,
2015
[ paper ]
- Combating Insider Attacks in IEEE 802.11 Wireless Networks with Broadcast
Encryption
Joseph Soryal, Irippuge Milinda Perera, Ihab Darwish, Nelly Fazio, Rosario Gennaro,
and Tarek Saadawi
IEEE Int. Conf. on Advanced Information Networking and Applications – AINA
2014, pp. 472-479, IEEE, 2014
[ paper | ieee ]
- Broadcast Steganography
Nelly Fazio, Antonio R. Nicolosi, and Irippuge Milinda Perera
Topics in Cryptology – CT-RSA 2014, LNCS 8366, pp. 64-84, Springer,
2014
[ paper | eprint | springer ]
- Hard-Core Predicates for a Diffie-Hellman Problem over Finite Fields
Nelly Fazio, Rosario Gennaro, Irippuge Milinda Perera, and William E. Skeith
III
Advances in Cryptology – CRYPTO 2013, LNCS 8043, pp. 148-165, Springer,
2013
[ paper | eprint | springer ]
- Protecting Receivers' Identities in Secure Data Distribution
Nelly Fazio and Irippuge Milinda Perera
The Annual Conference of International Technology Alliance – ACITA,
2012
[ paper | poster ]
- Outsider-Anonymous Broadcast Encryption with Sublinear Ciphertexts
Nelly Fazio and Irippuge Milinda Perera
Public Key Cryptography – PKC 2012, LNCS 7293, pp. 225-242, Springer,
2012
[ paper | eprint | springer | poster
]
Presentations:
- Combating Insider Attacks in IEEE 802.11 Wireless Networks with Broadcast
Encryption
AINA Conference, University of Victoria, BC, Canada, May 14, 2014
[ slides | listing ]
- Broadcast Steganography
RSA Conference, Moscone Center, CA, USA, February 25, 2014
[ slides | listing ]
- How to Broadcast a Secret Covertly
GC Cryptography Student Seminar, The Graduate Center of CUNY, NY, USA, February 21,
2014
[ slides | listing ]
- Hard-Core Predicates for a Diffie-Hellman Problem over Finite Fields
CRYPTO Conference, UC Santa Barbara, CA, USA, August 21, 2013
[ video |
slides | listing
]
- Challenges in Proving Hard-Core Predicates for a Diffie-Hellman Problem
IBM Research Cryptography Seminar, Thomas J. Watson Research Center, NY, USA, April
10, 2013
[ slides ]
- Anonymous Broadcast Encryption
GC Cryptography Student Seminar, The Graduate Center of CUNY, NY, USA, June 22,
2012
[ slides | listing
]
- Outsider-Anonymous Broadcast Encryption with Sublinear Ciphertexts
NYU Cryptography Seminar, New York University, NY, USA, April 25, 2012
[ slides | listing ]
Theses:
- Doctoral Dissertation: Theory and Applications of
Outsider Anonymity in Broadcast Encryption
Irippuge Milinda Perera
The Department of Computer Science, The Graduate Center of CUNY, 2015
[ paper ]
- Master's Thesis: Anonymity in Public-Key
Encryption
Irippuge Milinda Perera
The Department of Computer Science, The City College of CUNY, 2013
[ paper ]
- Senior Capstone Project: A Secure Communication System
for Sensor Networks
Tolulope Abayomi, Stanis Laus Billy, Edwin Guzman, and Irippuge Milinda
Perera
The Department of Computer Science, The City College of CUNY, 2010
[ paper ]
Technical Reports:
- Decentralized Information Flow Control for Operating Systems – A
Survey
Kenneth Ezirim, Wai Khoo, George Koumantaris, Raymond Law, and Irippuge Milinda
Perera
The Department of Computer Science, The Graduate Center of CUNY, 2012
[ paper ]
- Trusted Platform Module – A Survey
Kenneth Ezirim, Wai Khoo, George Koumantaris, Raymond Law, and Irippuge Milinda
Perera
The Department of Computer Science, The Graduate Center of CUNY, 2012
[ paper ]
- Defenses Against Network Coding Pollution Attacks in Wireless Mesh
Networks
Irippuge Milinda Perera
The Department of Computer Science, The Graduate Center of CUNY, 2011
[ paper ]
 |
|